


Castlevania III
Password Algorithm
Name-and-Password System · Special Names · Game State
Name Hash · Payload · Encoding · Decoding · All Passwords · Code
This article explains the mechanism Castlevania III: Dracula’s Curse uses to save and restore game state through the medium of passwords. The information discussed here applies to the North America and PAL versions released for the NES, not the Japanese version, Akumajō Densetsu, released for the Famicom.
Castlevania III employs a combined name-and-password system. At game start, the player is prompted to enter a name:

The name consists of 8 characters; names that appear shorter-than that are right-padded with spaces. The available character set includes the upper-case letters of the English alphabet, space, exclamation mark, question mark, and period. A completely blank name (8 spaces) is valid.
At game over, the player is presented with a choice: immediately continue from the last save point or encode the game state to a password, enabling play to resume sometime in the future.
Selecting “PASSWORD” displays a screen like the one below.

In this case, the name was set to “EXAMPLE”; it is shown in the box at the top of the screen. Directly below the name is a horizontal table containing the marks used in passwords: blank, whip, rosary, and heart. Below that is the password, a 4×4 matrix where each element is a mark. Note that passwords tend to be sparse matrices.
To persist the game state, the player uses a writing implement and some artistic skills to jot down the name and the password to paper. Upon completion, the player can turn off the NES, which wipes the system’s memory, game state and all.
To restore the game state, the player begins by selecting “PASSWORD” from the title screen:

As shown below, the player is prompted to enter the name associated with the password.

Next, the player is presented with the password entry screen:

The screen displays 2 cyan cursors, one for selecting the mark from the horizontal table and the other for placing the mark in the password matrix. The following image depicts an entered password.

Upon proper entry, the game resumes from the save point. However, the slightest error results in the following message.

This is typically due to a misplaced mark or failing to write down the name and forgetting what was used. The password only works for the name entered at game start.
5 special names affect gameplay:
| Name | Description |
|---|---|
| HELP ME | Start and continue with 10 lives. |
| AKAMA | Start in Hard Mode alone. |
| OKUDA | Start in Normal Mode with Alucard. |
| URATA | Start in Normal Mode with Sypha. |
| FUJIMOTO | Start in Normal Mode with Grant. |
Despite what the Angry Video Game Nerd demoed in his Castlevania (Part 2) video, “HELP ME” contains a space.
The “OKUDA”, “URATA”, and “FUJIMOTO” special names start Normal Mode with a partner, but they also force the player to stick with that partner for the rest of the game. Obtaining or exchanging partners is similarly disabled in Hard Mode. In the case of “AKAMA”, it means playing through Hard Mode, in its entirety, alone.
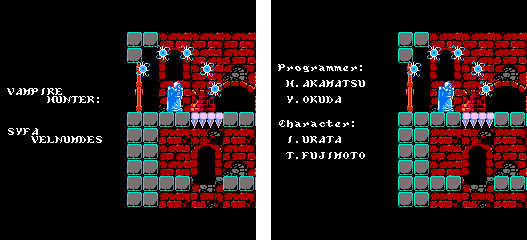
Some websites claim that using the name “GAMETEAM” along with a special password will start the player in Hard Mode. And if the player successively beats the game, real ending credits will display, revealing the actual team that made the game. This is true, but there is nothing special about the name-and-password combo. The alternate credits are the reward for beating Hard Mode, regardless of the name. Furthermore, the alternate credits reveal the origin of the special names:
Passwords encapsulate save point, partner, and mode. Those are the only properties of the game state retained when the player continues after game over. Everything else is reset.
After losing all lives, the player falls back to the most recent save point. This usually means restarting the current block (the level) from its beginning. But due to shortcuts and sub-bosses, this is not always the case, as revealed by the table below.
| Save Point | Block | Description |
|---|---|---|
| 00 | 1-1 | Warakiya Village - Skull Knight |
| 01 | 2-1 | Clock Tower of Untimely Death (climb up) - Nasty Grant |
| 02 | 2-4 | Clock Tower of Untimely Death (climb down to the Forest of Darkness) |
| 03 | 3-0 | Forest of Darkness (from the Warakiya Village) - Cyclops plus Sypha or Murky Marsh |
| 04 | 3-1 | Forest of Darkness (from the Clock Tower) - Cyclops plus Sypha or Murky Marsh |
| 05 | 4-A | Haunted Ship of Fools - Snake Man Sentinel and Death Fire (Mummies and Cyclops) |
| 06 | 5-A | Tower of Terror - Frankenstein's Monster |
| 07 | 6-A | Causeway of Chaos - Water Dragons |
| 08 | 4-1 | Murky Marsh of Morbid Morons - Giant Bat |
| 09 | 5-1 | Caves (entering) - Alucard |
| 0A | 5-6 | Caves (escaping) - Skull Knight King or Sunken City |
| 0B | 6-1 | Sunken City of Poltergeists - Bone Dragon King |
| 0C | 6-1 | Castle Basement - Frankenstein's Monster |
| 0D | 7-1 | Morbid Mountains - Giant Bat and Death Fire King (Mummies, Cyclops, and Leviathan) |
| 0E | 7-A | Rampart and Lookout Tower - Death Fire King (Mummies, Cyclops, and Leviathan) |
| 0F | 8-1 | Castle Entrance - Grim Reaper |
| 10 | 9-1 | Villa and Waterfalls - Doppelgänger |
| 11 | A-1 | Clock Tower and Castle Keep - Dracula |
There are 18 save points, indexed $00–$11. The names of the places and bosses are never mentioned within the game; the descriptions vary from source to source. Contrarily, the block and sub-block values appear in the HUD. All blocks start with a sub-block of 1 or A, except for the Forest of Darkness, which maybe entered from save points $03 or $04:

The only other mid-block save points are $02 and $0A, due to sub-bosses:
Save points $0B and $0C share common block values. But they are 2 totally different levels:

There are 4 values for partner, indexed 0–3:
| Partner | Name |
|---|---|
| 0 | none |
| 1 | Sypha Belnades |
| 2 | Grant Danasty |
| 3 | Alucard |
In Normal Mode, without a special name, a partner may only be used along a pathway of save points which starts when the partner is first encountered in the game. During password decoding, the save point and partner combination is checked against the table below. If it is an invalid combo, the password is rejected.
| Name | 00 | 01 | 02 | 03 | 04 | 05 | 06 | 07 | 08 | 09 | 0A | 0B | 0C | 0D | 0E | 0F | 10 | 11 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Sypha | × | × | × | × | × | × | × | |||||||||||
| Grant | × | × | × | × | × | × | × | × | × | × | × | × | × | × | × | |||
| Alucard | × | × | × | × | × | × | × |
This check is skipped for special names, except for “HELP ME”. The remaining special names lock the game into a specific partner from the beginning, or in the case of “AKAMA”, no partner.
In addition, decoding always uses the partner encapsulated in the password, not necessarily the one associated with a special name. For example, if a new game is started with “OKUDA”, the player immediately gets stuck with Alucard. However, a valid password can be constructed for “OKUDA” for any partner at any save point and mode. Normal gameplay would never display such a password. But it can be constructed and used, nonetheless.
The same applies to “AKAMA”, but Hard Mode is always used, regardless of the mode encapsulated in the password.
There are 2 values for mode, indexed 0–1:
| Mode | Name |
|---|---|
| 0 | Normal |
| 1 | Hard |
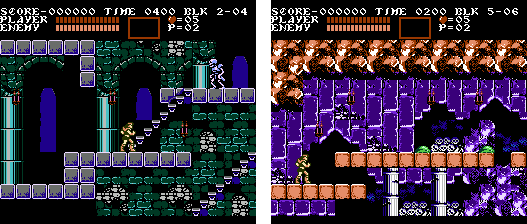
After beating the game in Normal Mode, it restarts in Hard Mode, which is considerably more difficult from the get-go. There are more enemies, they move faster, and they cause more damage. Below, one of the first screens of Normal Mode is on the left. Its Hard Mode counterpart, featuring additional enemies, is on the right.

The partner paired with the player at the end of Normal Mode carries over into Hard Mode. However, the ability to exchange partners is disabled in Hard Mode; the player is stuck with the same partner indefinitely or no partner at all if Normal Mode was beaten alone.
After beating the game in Hard Mode, it restarts, but not in some harder mode. There are only 2 mode and Hard Mode loops endlessly.
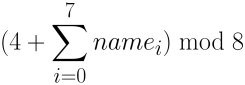
Rather than encapsulating the entire 8-character name, the password merely contains a 3‑bit hash. The hash is computed by adding 4 to the sum of all the character values and taking modulo 8 to produce a value in the range 0–7:
Interestingly, the game code uses a table to add different constants to the running sum based on the index of the loop:
; hashName() ; out: A = name hash (0--7) 03:B6CD LDA #$00 03:B6CF STA $0000 ; sum = 0; 03:B6D1 TAX 03:B6D2 LDA $07F8,X ; for (X = 0; X < 8; ++X) { 03:B6D5 CLC 03:B6D6 ADC $B6E6,X 03:B6D9 CLC 03:B6DA ADC $0000 03:B6DC STA $0000 ; sum += name[X] + NAME_HASH_SEEDS[X]; 03:B6DE INX 03:B6DF CPX #$08 03:B6E1 BNE $B6D2 ; } 03:B6E3 AND #$07 ; A = sum % 8; 03:B6E5 RTS ; return; ; NAME_HASH_SEEDS ; Due to the modulo operation, this table is pointless; the values can be tallied ahead of time. However, the ; intention may have been to apply this table only to the nonblank characters. But that check is not there. 03:B6E6 .byte $07, $03, $01, $06, $02, $04, $05, $00
As noted in the comment, the table is pointless. The intention may have been to add constants only for the nonblank characters. And, for whatever reason, the check was left out.
The character values are tile indices of the Pattern Table. As shown below, A–Z, followed by exclamation mark and question mark, correspond to $50–$6B. Period is $4B. And space is $00.

Special names are hashed the same way as any other name. The same is true for a blank name, which is represented as 8 spaces.
The password encapsulates a 1-byte payload and a 1-byte payload hash.
The payload byte contains the mode (bit 0), the partner (bits 1–2), the toggle mask index (bit 3), the least significant bit of the save point (bit 4), and the name hash (bits 5–7):
76543210 -------- NNNSTPPM ││││││││ │││││││└─ mode │││││└┴── partner ││││└──── toggle mask index │││└───── save point bit-0 └┴┴────── name hash
The toggle mask index is set randomly during password generation. It affects how the hash of the payload is computed. Since there are 2 possible values, there exists 2 valid passwords for a given name, partner, and mode. For example, if the player starts a new game with a blank name and repeatedly get game over in the first block, the game will eventually reveal a pair of equivalent passwords:

The payload hash exists to safeguard the integrity of the payload. During decoding, it is used to detect errors that may have been introduced while writing down or entering the password. It also makes it exceedingly improbable to guess valid passwords.
To compute the payload hash, the following steps are performed:
The steps above describe a one-way hash function. There is no way to recover the payload from its hash.
Within the password matrix, the payload and its hash are represented as a string of 8 marks. Each mark is a 2‑bit value that can be interpreted using the table below.
| Mark | Name |
|---|---|
| 0 | blank |
| 1 | whip |
| 2 | rosary |
| 3 | heart |
Within the string representation, the ith mark is the concatenation of the ith bit of the payload byte and the ith bit of the hash byte. In other words, the payload provides the high bits and the hash provides the low bits. They are paired up for each bit index to make a mark.
Encoding is the process of converting a name and a game state into a password. It involves the following steps.



Decoding is the process of converting a name and a password into a game state. It involves the following steps.



An unbridged table of all 3,294 valid name-and-password combos is located here.
Each column corresponds to a save point. Each row corresponds to a unique combination of name, partner, toggle mask index, and mode. Since the name is hashed to a 3‑bit value, there are only 8 name classes. As shown in the table below, the shortest names that cover all the classes are blank and B–H. These names appear at the left of each row.
| Name | Hash |
|---|---|
| (blank) | 4 |
| A | 4 |
| B | 5 |
| C | 6 |
| D | 7 |
| E | 0 |
| F | 1 |
| G | 2 |
| H | 3 |
| HELP ME | 1 |
| AKAMA | 2 |
| OKUDA | 3 |
| URATA | 4 |
| FUJIMOTO | 1 |
The table includes the special names because they modify the behavior of the game.
The white names and red names correspond to Normal Mode and Hard Mode, respectively. “AKAMA” only appears in red because it imposes Hard Mode regardless of the mode encapsulated within the password. But the “AKAMA” passwords encapsulating Normal Mode are still valid and they appear in the table for completeness.
The sprites at the left of each row indicate partner.
Toggle mask index is indicated by the direction Trevor faces: right is 0 and left is 1. Toggle mask index does not affect gameplay. But it does double the number of valid passwords.
The gaps in the table correspond to invalid save point and partner combinations. In Normal Mode, without a special name, a partner may only be used along a pathway of save points which starts when the partner is first encountered in the game.
The special names, other than “HELP ME”, lock the player into a particular partner. However, the partner encapsulated within the password takes precedence over the one associated with the special name. Consequentially, the special names appear with all partner combinations in the table.
For more details, check out the segments of the game code related to password encoding and decoding here. A copy can also be found in this repository.
The Java program that generated the unabridged password table is located here.
|
Copyright © 2021 meatfighter.com |